F-Secure Threat protection for your business
For us, not only the product qualities, but also the company successes clearly spoke in favor of a partnership.
F-Secure Countercept - defends companies against all targeted attacks
Founded in 1988 by Risto Siilasmaa as Data Fellows Corporation in Helsinki, the company has been working on data security from the beginning. The founders recognized the enormous and dynamically growing market, targeted the focus and served it with a range of products called F-Secure. It was a logical step to use the now internationally established name for the company itself – the renaming took place in 2000.
Listed on NASDAQ OMX, Helsinki since 1999, the company currently has more than 1,600 employees in more than 20 offices and research facilities worldwide. With a turnover of 158 million euros (2016), a profit of 19 million euros (2016) could be recorded. The number of users rose in the private sector in the tens of millions, and trust more than 100,000 corporate customers the F-Secure products. For us, not only the product qualities, but also the company successes clearly spoke in favor of a partnership.
Our award-winning solutions use cutting edge technology, heuristic analytics and advanced learning algorithms to fully secure all your devices.
Corporate development and orientation of F-Secure
Again F-Secure conquered antivirus protection market, especially with the successful deployment of multiple virus scanning engines in one application. The simultaneous monitoring significantly increased the detection rate of harmful programs. Initially, Frisk Software and Kaspersky’s scanning engines were used, but later the company relied on the Aquarius-designated Bitdefender virus scan engine, which is combined with a proprietary search algorithm. These in-house developments are known as Gemini, Hydra and DeepGuard.
F-Secure was able to distinguish itself in a broader field beyond anti-virus, such as BlackLight as an application for detecting and removing kernel rootkits on Windows. In 2006, the company responded to a number of issues that, for example, led Sony to headline the issue of CD copy protection camouflaged by PC owners: BlackLight looks for files, processes, and folders that were originally intended to be hidden from the user , These are not only displayed, but also the relevant information is provided.
Another milestone in the company’s development was the topic of SSH encryption. For its merits, F-Secure was even awarded by the Finnish government, but concentrated again in 2004 on the original business field antivirus. The Encryption area was successfully handed over to WRQ, Inc.

F-Secure virus protection and more - the products at a glance
So today we can access specialized knowledge: The product portfolio includes effective solutions that protect not only PCs and servers, but also mobile devices against attacks by viruses, Trojans, worms, phishing and spam programs. In addition, programs and apps are offered that secure e-mail and Internet gateways. F-Secure has the reputation of being able to react quickly to newly detected viruses with updates and virus removal tools. When set up, the company serves the needs of a diverse audience ranging from home users and businesses to Internet service providers or mobile service providers.
Endpoint protection made by F-Secure
From our point of view, the issue of endpoint protection is of enormous importance, especially as experience shows that the infrastructure in companies is growing rapidly and unclearly – the topic of security often does not come fast enough after all. In view of the cyber threats, which are increasing exponentially not only in terms of volume but above all of complexity, vulnerable points of attack are quickly opening up. It is all the more important not only to stand up against known threats, but also to be prepared for future challenges such as data loss via mobile devices or ransomware.
The demands on the IT departments are therefore high, they should protect the infrastructure effectively, but can usually use only limited resources. At the same time, the entrepreneurial capacity to act must not be restricted. What sounds like squaring the circle can be realized with F-Secure’s flexible, tailor-made applications. There are two basic variants to choose from, each of which consists of different components and can therefore be individually adapted.


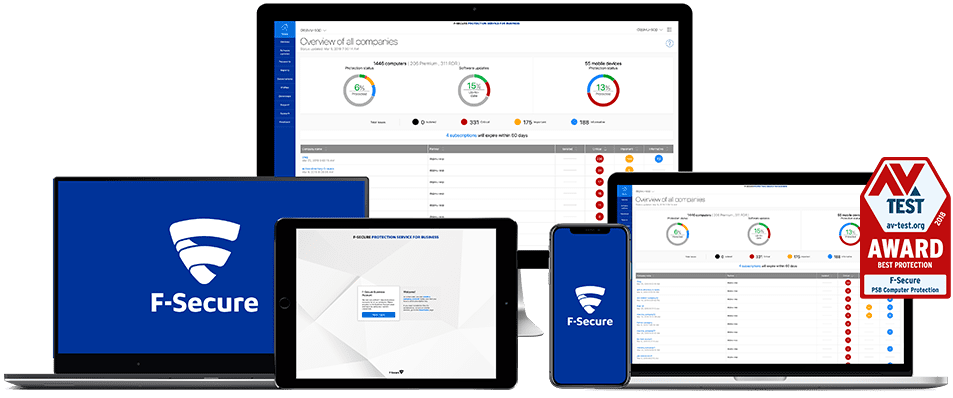
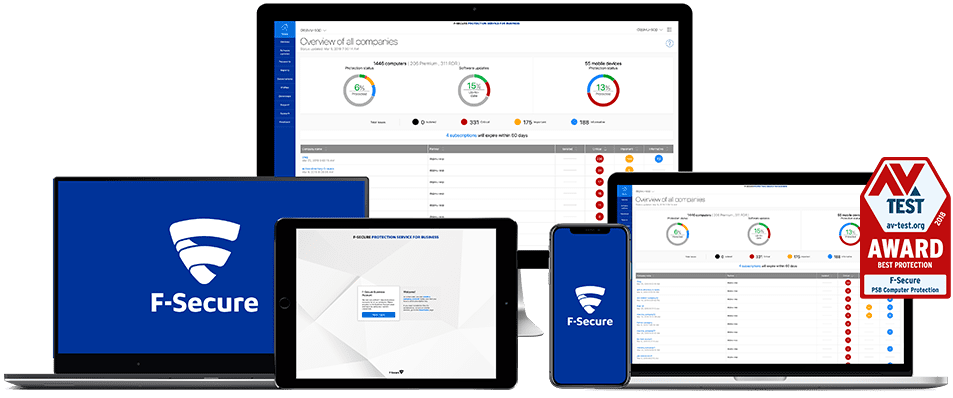
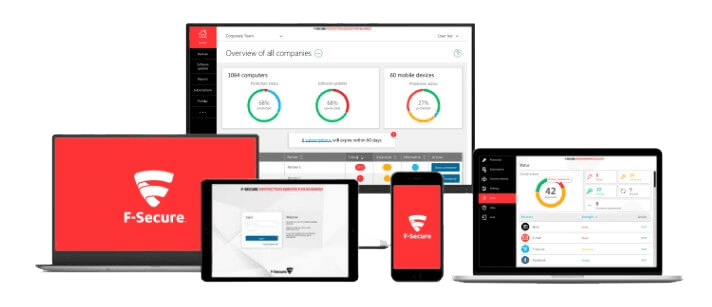
Protection service for companies
One solution is hosted in the cloud – a comprehensive yet flexible endpoint protection that provides effective protection against any threat. The already outstanding defenses are thus further improved by the extensive use of artificial intelligence, machine algorithms and heuristic analyzes. Neither malware, phishing or ransomware have a real chance with this comprehensive protection.
All devices are covered – regardless of whether they are Windows, Mac or mobile devices. But for F-Secure, complete security also means not only blocking all harmful activity, but also identifying other dangers. These include, for example, weak passwords or missing security paches for third-party software. The big advantage: You do not have to combine different products to implement such a security strategy, but can realize all security requirements in one:
- Computer Protection
- Mobile Protection
- Server security
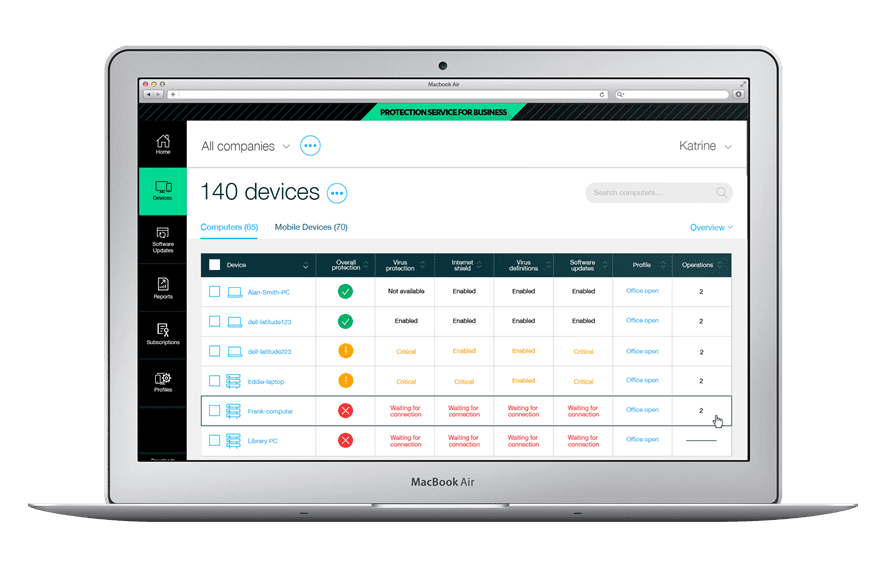
- management portal
- Password protection
All security functions are available for the entire infrastructure and can be easily operated via the intuitive user interface – without sound cyber security expertise.
Business Suite
The equivalent alternative will be provided on site. This variant of the security solution can also be configured as required – from the gateway to the end device. The difference is that you implement these applications directly into your IT infrastructure. The range of security solutions includes, for example
- Client Security
- Client Security for Mac
- Linux Security
- Server security
- E-mail and server security
- Virtual Security
- Policy Manager
Based on a detailed analysis, all security functions can be mapped and handled.
What are your security requirements?
We meet your organization’s IT security needs – from industry-leading endpoint protection to cyber security strategies and incident response.